Cybersecurity doesn’t stand still—and neither can your compliance evidence.
Modern vehicles and robots ship as software-defined systems, where new vulnerabilities, new exploit techniques, and new supplier updates appear continuously. Regulations and standards reflect that reality: UN R155 expects manufacturers to keep risk assessments current, continually monitor for vulnerabilities, and reassess the effectiveness of controls as new threats emerge—while respecting privacy and consent when using vehicle data and logs.
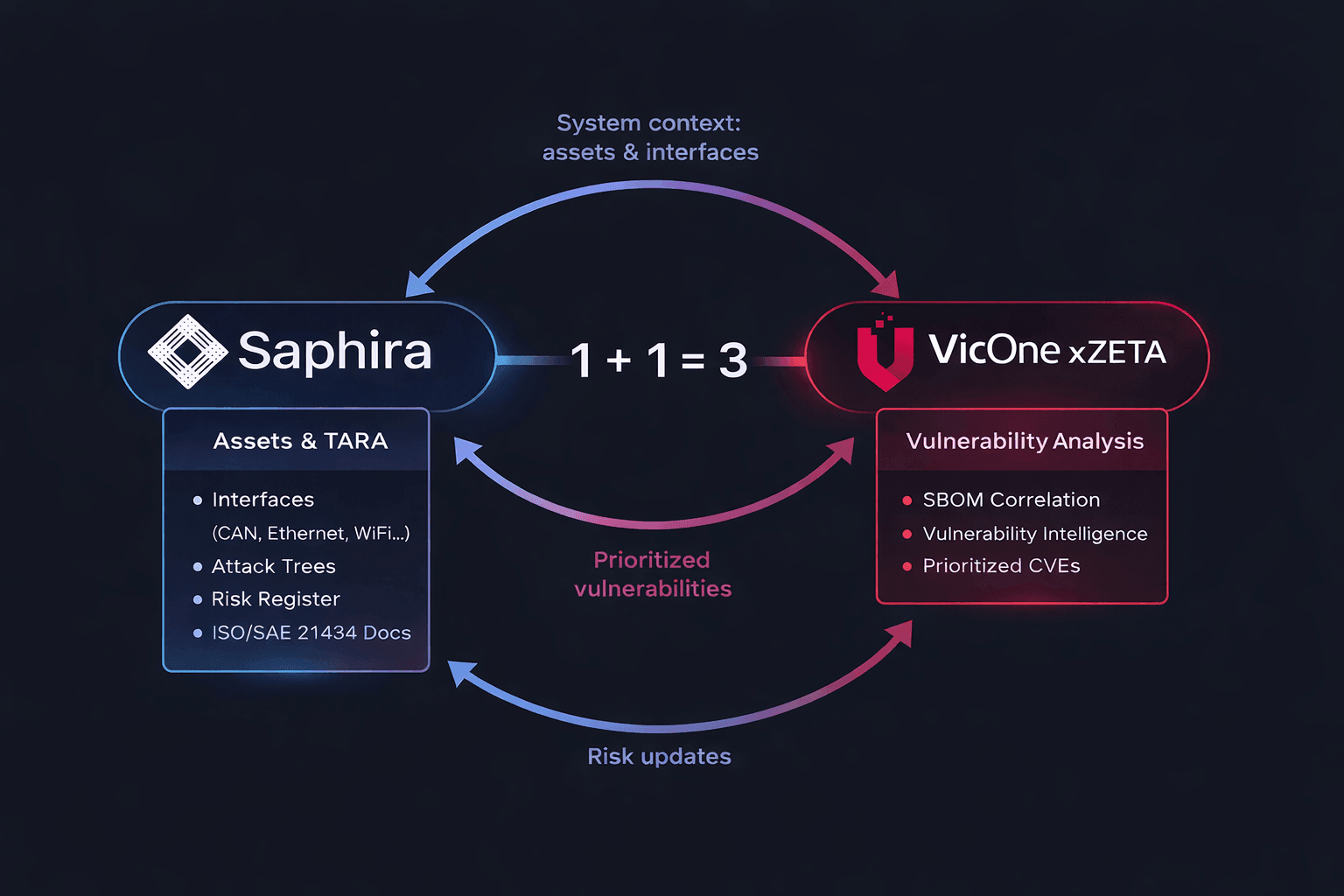
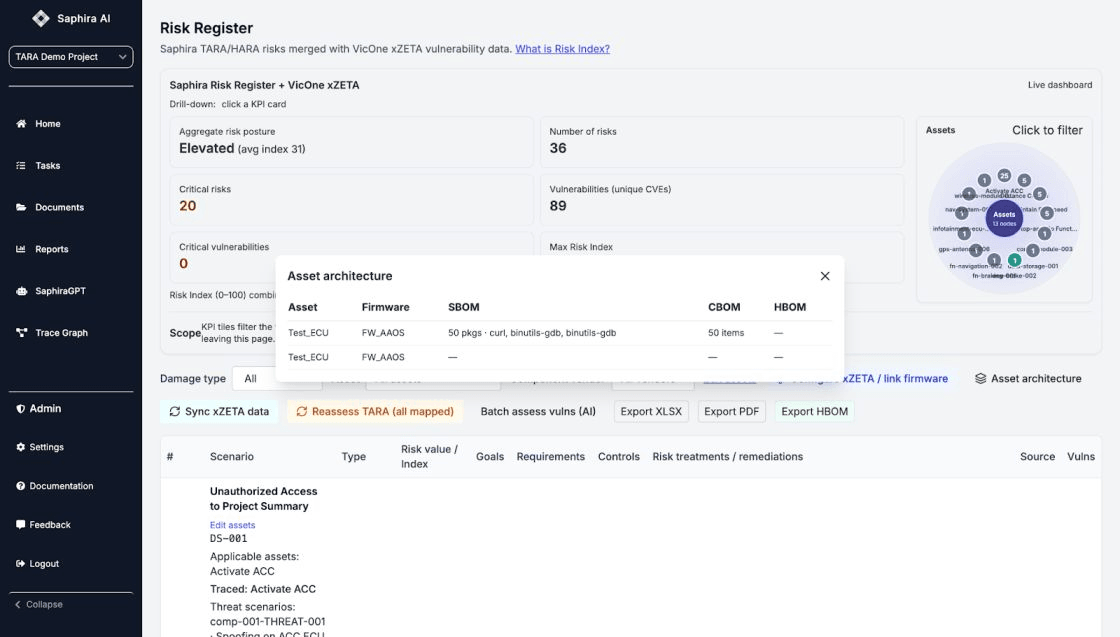
Today, we’re excited to announce a partnership between Saphira and VicOne to make that “continuous” mandate practical: new vulnerabilities detected in VicOne can automatically trigger a fresh TARA in Saphira, updating your cybersecurity documentation into a continuously maintained, audit-ready living document.
What we’re building together: circular automation
Most teams run two parallel motions:
- Vulnerability management finds issues (often at high volume)
- TARA and cybersecurity case documentation gets updated periodically—sometimes only when an audit or release gate forces it
That gap is where risk hides.
With Saphira × VicOne, we’re closing the loop:
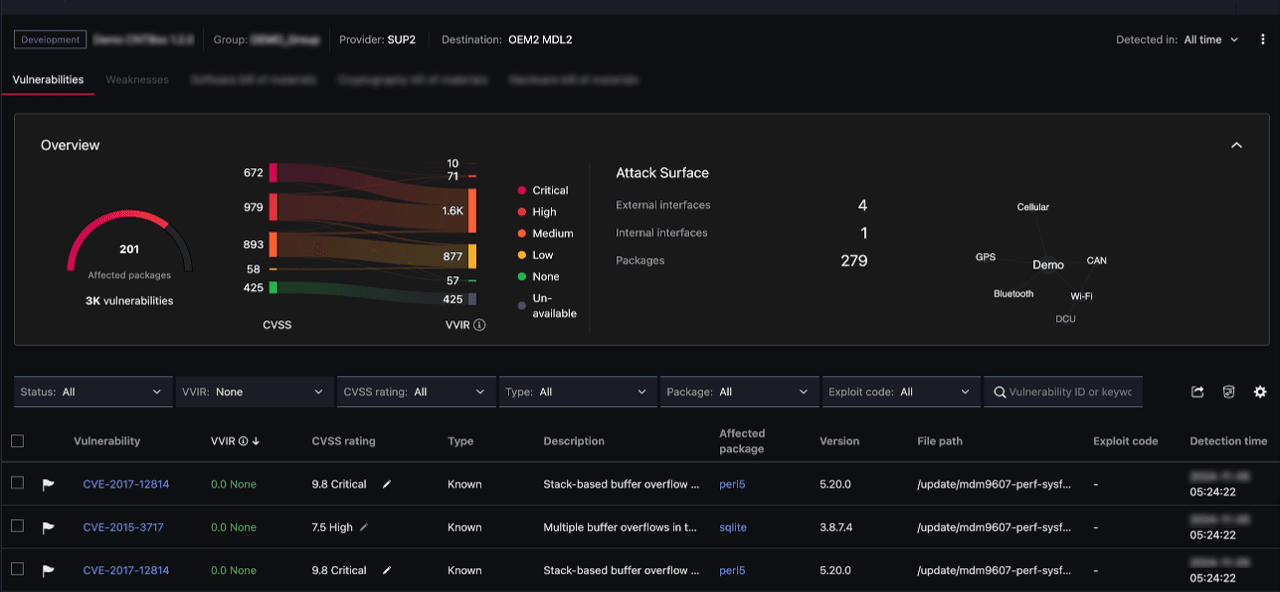
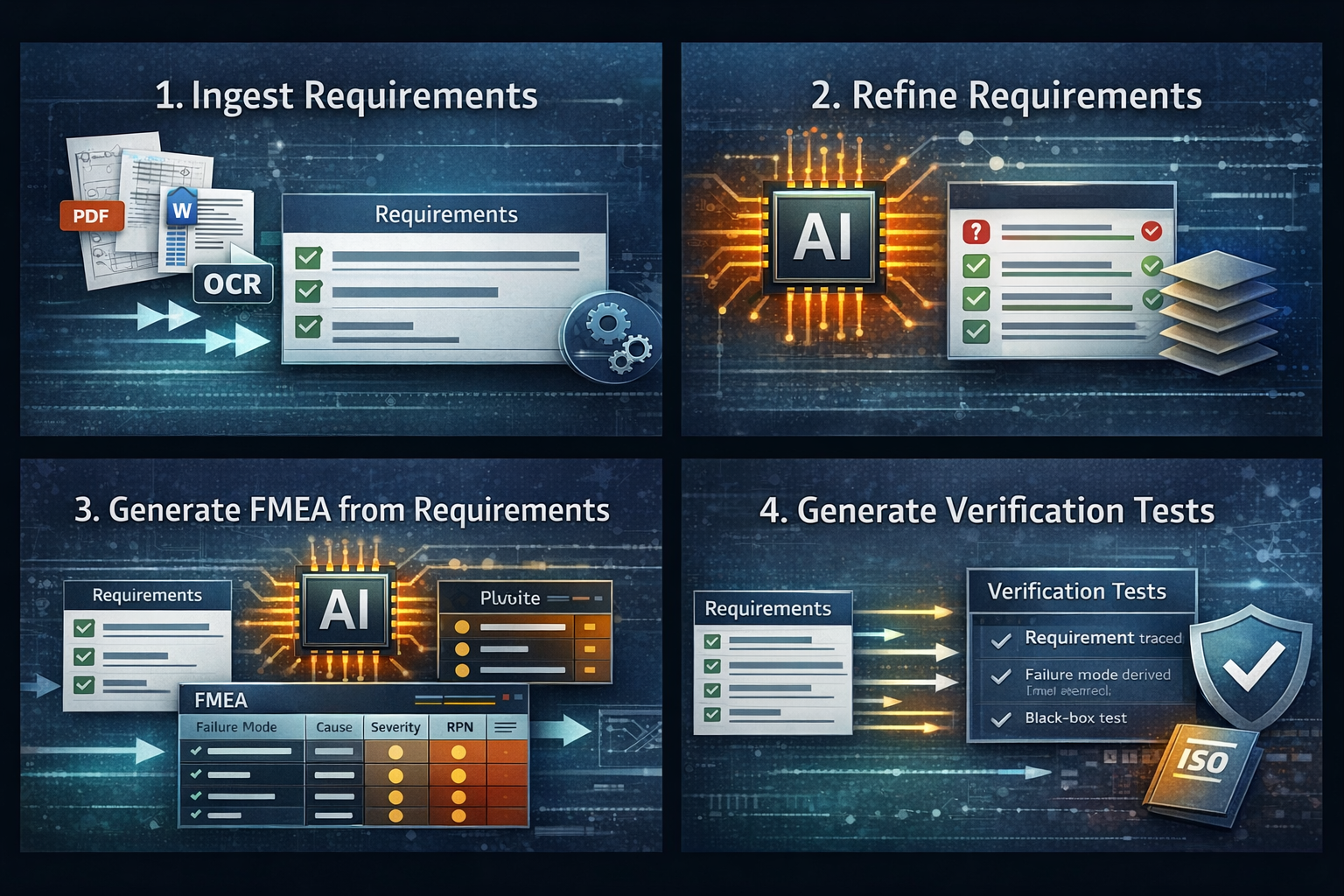
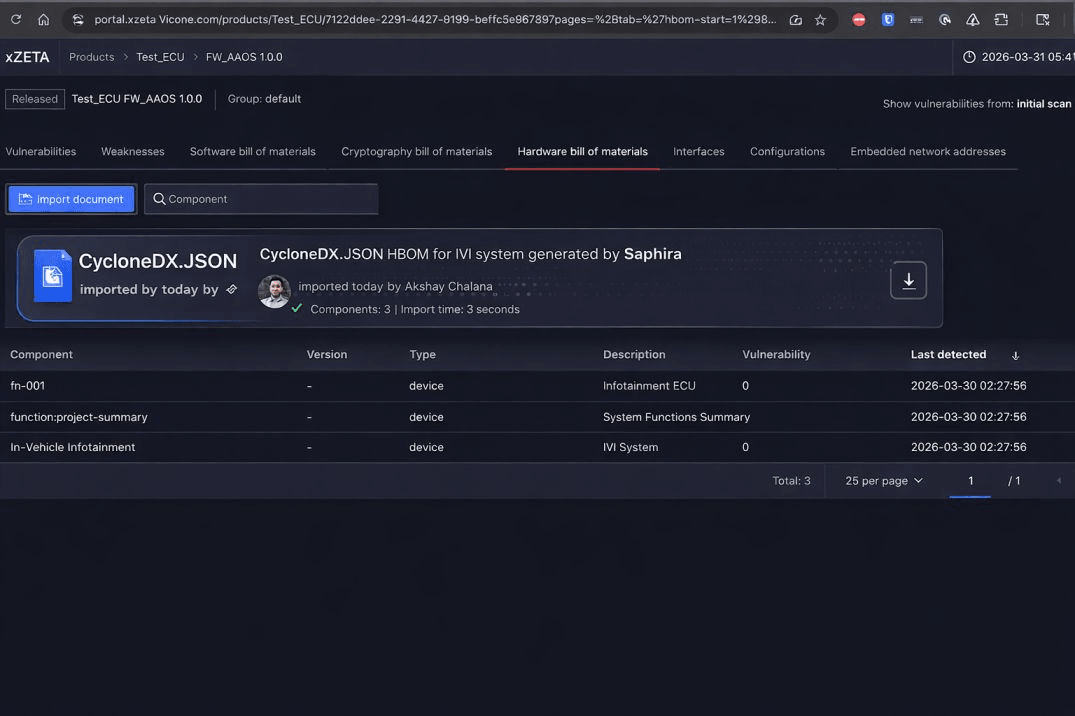
- VicOne xZETA detects and contextualizes vulnerabilities using SBOM-based insights and advanced threat intelligence—including zero-day and undisclosed vulnerabilities—integrated into CI/CD workflows for automation.
- When a vulnerability affects a component in your product, VicOne triggers an event to Saphira (e.g., via API/webhook).
- Saphira automatically refreshes the relevant TARA work products—from impacted assets and attack paths to updated risk, cybersecurity goals, and requirements—aligned to ISO/SAE 21434 workflows and cybersecurity case evidence.
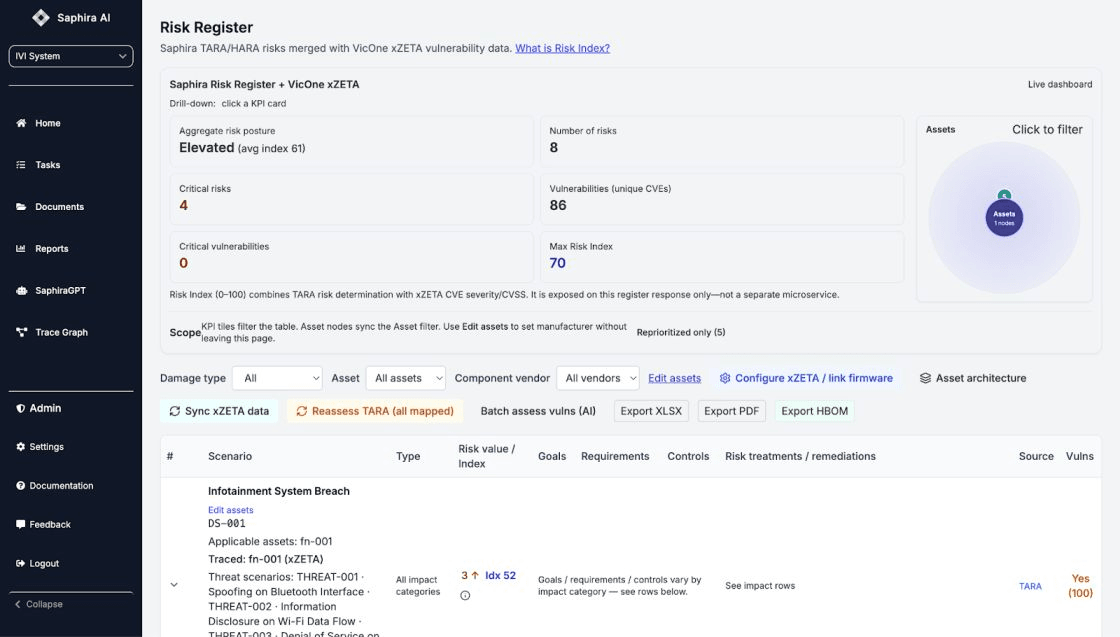
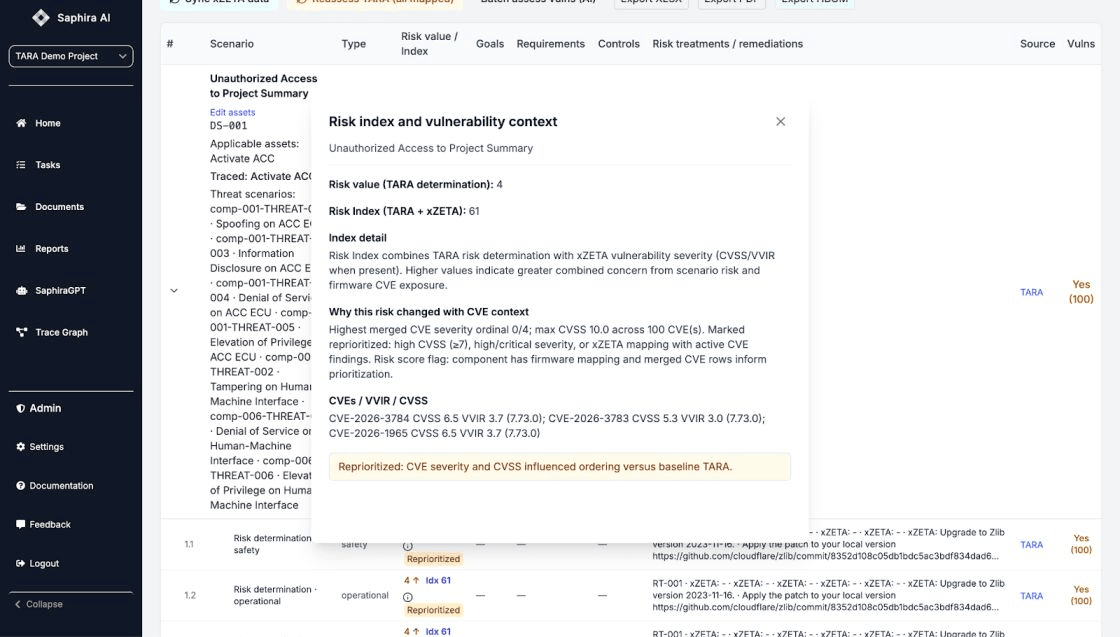
- Saphira then feeds the impact analysis back to VicOne, so vulnerability response can be prioritized using real engineering context—not severity scores alone.
The result: vulnerability intelligence and TARA stop being separate artifacts. They become a continuously updating system.
How the integration works (simple technical view)
At the center is a shared “language”:
- SBOM-based component identity (e.g., SPDX/CycloneDX) to map vulnerabilities to what’s actually in the build
- Standard vulnerability identifiers (CVE/CWE), plus severity signals (CVSS), with VicOne’s Vulnerability Impact Rating VVIR enabling prioritization of what matters most
- Model-driven architecture + assets + attack paths inside Saphira’s ISO/SAE 21434-aligned TARA workflow
Security and governance are built in:
- integrations use common enterprise patterns (scoped tokens, RBAC, audit logs), and xZETA explicitly supports role-based access control
- organizations can apply sensible automation gates (e.g., auto-run reassessments for high-impact vulnerabilities and require human approval for risk treatment decisions)
Why this matters (benefits you can measure)
For OEMs, the biggest win is eliminating documentation drift: the cybersecurity case is continuously refreshed as vulnerabilities evolve—supporting UN R155 expectations that risk assessments stay current.
For Tier suppliers, you can respond faster and deliver better evidence packages across multiple programs—without duplicating TARA work by hand. VicOne xZETA emphasizes actionable vulnerability insights and SBOM automation; Saphira emphasizes traceable TARA outputs and exportable work products.
For robotics companies, you get the same closed loop for connected robots deployed in factories and the field—where security issues can quickly become safety and availability issues. Saphira is built to support certification workflows across robots and vehicles and emphasizes continuous monitoring and early gap detection.
And because this loop is instrumented, you can prove impact with KPIs:
- time from vulnerability discovery → updated TARA and documentation
- time from discovery → remediation ticket created
- reduction in audit prep time
- improvement in traceability completeness for high-risk threats
Real-world scenarios
- Automotive OTA: a new vulnerability affects an update component; the TARA refresh happens automatically before release gates slip
- Factory robots: a vulnerability in a network-exposed controller library triggers a re-assessment tied directly to safety-critical motion functions
- Autonomous systems: shared compute platforms across variants get continuously updated risk documentation as the vulnerability landscape changes

When VicOne identifies a new vulnerability, Saphira automatically triggers a new TARA analysis, updates cybersecurity documentation, and generates mitigation actions—creating a continuous cybersecurity loop.
Call to action
If you’re responsible for cybersecurity engineering, product security, or compliance in automotive, suppliers, or robotics, and you’re tired of treating TARA as a static document—let’s talk.